How to Use tcpdump Filter IP Address: A Beginner’s Guide
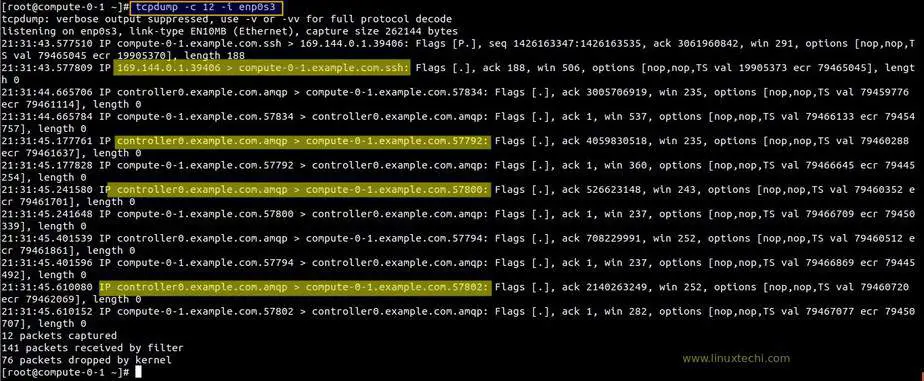
You will be surprised to learn what a command line tool can do to convey network traffic and similar data to you. For example, tcpdump is one of the most used command line tools for UNIX-based computers such as Linux and macOS. And, it can capture the network traffic can show it on the display or save it.
Network engineers, cybersecurity experts, and system administrators use this command-line tool for the following reasons:
- Resolving network issues
- Understanding network protocols
- Examining suspicious network activity and so on
However, tcpdump can produce too much output that users might struggle to locate the information he or she is looking for. Therefore, you can try tcpdump filter IP addresses to find the network traffic of your interest. Let’s dig out more about tcpdump filter expressions and much more.
What are Different Types of tcpdump Filter IP Addresses?
For tcpdump, multiple filtering expressions are available that will help you to limit the network traffic captured, shown, or saved.
Here are the major tcpdump filter IP address types that you might find useful:
- Host filters
- Port filters
- Network filters
- Protocol filters
- Negating a filter match
- And, combining filters
Apart from working with essential filters, tcpdump uses some particular flags or options for modified or enhanced outputs.
Here are some frequently used flags for the tcpdump command-line tool:
- -i: To listen on the mentioned interface.
- -n: This flag doesn’t perform reverse DNS resolution on IP addresses or resolve hostnames.
- -X: This displays the packet’s content in both ASCII and hex.
- -t: To print human-accessible timestamp in every dump command line.
- -s: This particular flag tells the size or snap length of the data captured in bytes. You can use -s) to capture every single data.
- -q: To display less protocol information.
- -S: This will print absolute sequence numbers.
- -c N: This will get you only N number of packets and then it will terminate.
- -v: To enable verbose logging or details output (this conveys to users how many packets are captured).
- -w: To write the raw traffic packets to files.
- -e: To print link-layer header on every line.
- -G rotate_seconds: To generate a new file each time the mentioned number of seconds has passed.
Now, let’s proceed to the major tcpdump filter IP address types and examples:
Host Filters
If you want to filter a particular host, add the ‘host’ word and the IP address to the tcpdump command line. For instance, to tcpdump filter IP address 192.168.1.110, try the following command:
# tcpdump -ni igb1 host 192.168.1.110
This will start capturing all the traffic from and to the specified host. Additionally, you can capture traffic only initiated by the host. Here’s the required command line that you need to execute:
# tcpdump -ni igb1 src host 192.168.1.110
So, appending src will do the intended job of finding the traffic from the source to the specific host. On the other hand, you can find out the traffic destined for the same IP address by performing the command line with dst:
# tcpdump -ni igb1 dst host 192.168.1.110
See, it’s easy to use tcpdump host filter expressions and use them for more straightforward network traffic information.
Port Filters
Sometimes, it’s insufficient to curb the host so that you can eradicate non-essential traffic from the captured data. On the other hand, the source or destination traffic might be useless. Instead, you might be interested in capturing all the network traffic of a distinct type.
Well, tcpdump filter IP address expressions can minimise redundancy with port filtering options. You can utilise port directives to filter on UDP and TCP ports. Now, this can capture UDP and TCP traffic with the particular port as a source or a destination port.
Users can append such port filters to state the protocol and src or dst to confirm whether it’s a source or destination port. For example, you have to implement the following command to get all HTTP traffic of port, 53:
# tcpdump -ni igb1 tcp port 53
On the other hand, try the command below to capture all DNS traffic (this is usually UDP but a handful of queries utilise TCP):
# tcpdump -ni igb1 port 80
Network Filters
If you want to narrow down the traffic capture to a definite subnet, then network filters are a must for your next tcpdump command execution. Just add ‘net’, and then you can specify the following types of the subnet, for example:
- CIDR-masked network (192.168.0.0/24)
- Dotted triple (192.168.0)
- Dotted quad (192.168.0.1)
- A Dotted pair (192.168)
- Or, a number (192)
Not to mention, a dotted quad is the same as a host, whereas a fitted triple will identify a subnet mask of 255.255.255.0. In addition, a dotted pair indicates a subnet mask of 255.255.0.0, and a single number implies a subnet mask of 255.0.0.0. Now, how to use network filters for tcpdump filter IP addresses?
Well, you can use the below-mentioned command line to show traffic from ir to any hosr with an address 192.168.0.x IP:
# tcpdump -ni igb1 net 192.168.0
However, the next command can capture network traffic from or to any host with an IP address of 20.x.x.x:
# tcpdump -ni igb1 net 20
The above-mentioned examples are the perfect command lines to capture traffic from or to a particular network. Moreover, you can incorporate the keywords such as src and dst along with host filters to specify the intended network.
For instance, you can consider the following command:
# tcpdump -ni igb1 src net 20
In addition, you can try the same for a CIDS mask address as an argument to the net:
# tcpdump -ni igb1 src net 192.168.0.0/12
Protocol Filters
Apart from the host, port, and network filters, you can filter specific protocols by utilising the protocol directive or the standalone protocol name. How can you tcpdump filter IP addresses based on protocols? For example, you can execute the following command to display all the ICMP traffic on the interface of igb1:
# tcpdump -ni igb1 icmp
Additionally, you can do the same for the following network protocols, such as:
- IGMP
- IGRP
- AH
- PIM
- CARP
- UDP
- ESP
- VRRP
- TCP
On the other hand, normal protocol names should be escaped with one or two backslashes when you use them with the proto directive, relying on the shell. This is because the default shell in pfSense software needs 2 backslashes to escape the protocol name.
For example, you can implement the following command with the Proto directive if you want to display traffic on the IGRP protocol:
# tcpdump -ni igb1 proto \\igrp
Or, you can skip the Proto directive and those 2 backslashes, like:
# tcpdump -ni igb1 -T carp carp
Negating a Filter Match
Do you want to reverse the function of a tcpdump filter IP address expression? If yes, you can try the ‘not’ keyword before the filter expression. For instance, if you might want to troubleshoot other protocols rather than ICMP then the command line should be as follows:
# tcpdump -ni igb1 not icmp
Similarly, you can opt for the following command if you wish to troubleshoot other protocols rather than CARP:
# tcpdump -ni igb1 not carp
Combining Filters
Is it possible to use combined tcpdump filter expressions? Yes, it is. In fact, you can combine any of the previously mentioned filters to get more streamlined outputs from the network traffic. You can combine them with keywords like ‘and’ and ‘or’.
For instance, here’s how you can display every HTTP traffic to and from 192.168.1.20:
# tcpdump -ni igb1 host 192.168.1.20 and tcp port 80
On top of that, the following command will show all HTTP traffic from different hosts or multiple hosts (either 192.168.1.10 or 192.168.1.25):
# tcpdump -ni igb1 host 192.168.1.10 or 192.168.1.25 and tcp port 80
Heads-Up on the Usage of tcpdump Filters
No doubt, using filter expressions and tcpdump command lines make the results more convenient to understand and find important details. However, you must pay special attention while using filters and flags within a single command line. Escaping a protocol or incorrectly ordering such components won’t achieve the desired result.
For instance, you will receive a syntax error after running the following tcpdump filter IP address command line:
# tcpdump -ni ogb1 -T carp carp -c 2
This incorrect order will throw you a syntax error as soon as you execute it. So, what is the correct order? Here it goes:
# tcpdump -ni igb1 -T carp -c 2 carp
Wrapping up…
What type of network troubleshooting is possible with tcpdump filter IP address expressions? Well, network administrators and experts have mentioned that they are incredibly useful in resolving port forwarding problems, IPsec tunnels not connecting, traversing traffic using an IPsec tunnel, outbound NAT, and more.
We hope that this guide introduced you to tcpdump filters and a basic idea of how to use them. You can review more resourceful information to find more practical use cases of tcpdump filters.
